Introduction Mutillidae II, an intentionally vulnerable web application, stands as a cornerstone in the realm of web security training. Developed by OWASP, it offers a safe and legal environment for individuals to explore common web vulnerabilities, ranging from SQL...
Sandbox99 Chronicles
From My Sandbox to Yours — Practical IT Insights.
Author: Jose Mendez
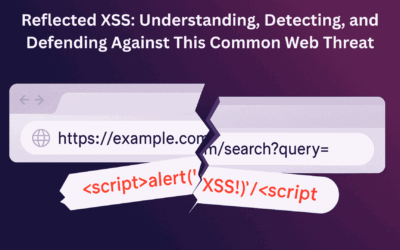
Reflected XSS: Understanding, Detecting, and Defending Against This Common Web Threat
Understanding Reflected Cross-Site Scripting (XSS) Reflected XSS is a common web security vulnerability that occurs when a web application takes user-supplied input and immediately returns it in an unvalidated or unfiltered form, leading to the execution of malicious...
Penetration Test Reports: Why There’s No “One Size Fits All”
Penetration Testing Reports: Unpacking the "Standard" Debate In my previous blog, "Why Penetration Test Reporting is Your Most Critical Deliverable," we delved into the profound value of a well-crafted penetration test report. It's not merely a formality; it's the...
Preparing for TryHackMe’s Junior Penetration Tester (PT1) Certification
The Golden Ticket: Becoming a Tester for TryHackMe's New PT1 Exam! Exciting news in the world of cybersecurity! TryHackMe, the awesome platform for hands-on learning, recently announced they were on the hunt for candidates to put their brand new Junior Penetration...
Living with the Epix Gen 2: Beyond the Unboxing Hype
Living with the Epix Gen 2: Beyond the Unboxing Hype I remember it like yesterday: April 2023, Browse a popular mall here in Metro Manila. I wasn't really looking for a new gadget, but then I spotted it – the Garmin Epix Gen 2, the very last unit, boasting a tempting...
Your Web App’s Shield: The 12 Phases of Web Penetration Testing Explained
In today's digital world, web applications are the backbone of businesses, from e-commerce sites to internal management systems. But as their importance grows, so does the risk of cyberattacks. This is where Web Application Penetration Testing (WAPT) comes in – it's a...